
Services Offered
Comprehensive cybersecurity solutions tailored to protect industrial control systems and critical infrastructure from evolving threats.
Our Comprehensive Services
At ICS Security Trust, we offer a wide range of specialized cybersecurity services designed to address the unique challenges faced by industrial environments. Our expert team provides end-to-end solutions to protect your critical infrastructure.
Industrial Cyber Risk Assessment
Our specialized risk assessment service is designed for industrial environments, identifying vulnerabilities across SCADA, ICS, DCS, and segmented network zones (e.g., DMZ). We focus on embedded systems and evaluate risks across hardware, firmware, and software layers to ensure robust protection.
Key Benefits
- End-to-end risk visibility from hardware to firmware and software
- Identification of attack vectors targeting embedded and OT systems
- Exposure analysis across SCADA, ICS, DCS, and perimeter zones
- Alignment with IEC 62443-4-2 and IEC 62443-3-3 cybersecurity requirements
Our Process
- 1Comprehensive system inventory and architecture mapping (SCADA, ICS, DCS, DMZ)
- 2Multilayer vulnerability analysis (HW/FW/SW) of embedded and operational systems
- 3Threat modeling based on OT-specific attack databases and tactics
- 4Prioritized risk reporting and mitigation roadmap aligned with IEC 62443
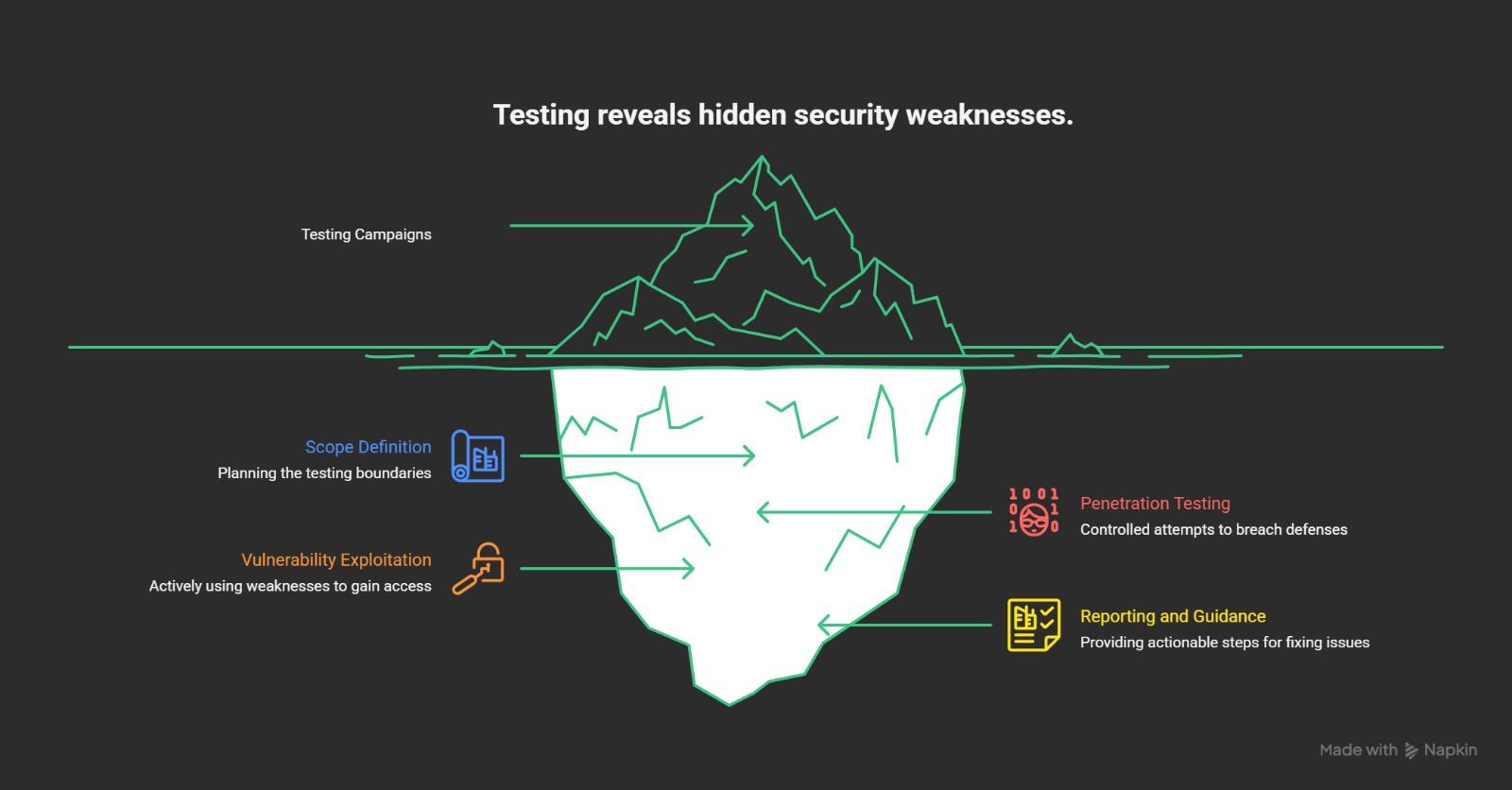
Testing Campaigns
Our testing campaigns simulate real-world attacks to evaluate the resilience of your industrial systems and identify security weaknesses before they can be exploited.
Key Benefits
- Identification of exploitable vulnerabilities
- Validation of existing security controls
- Realistic assessment of security posture
- Actionable recommendations for improvement
Our Process
- 1Scope definition and planning
- 2Controlled penetration testing
- 3Vulnerability exploitation attempts
- 4Detailed reporting and remediation guidance
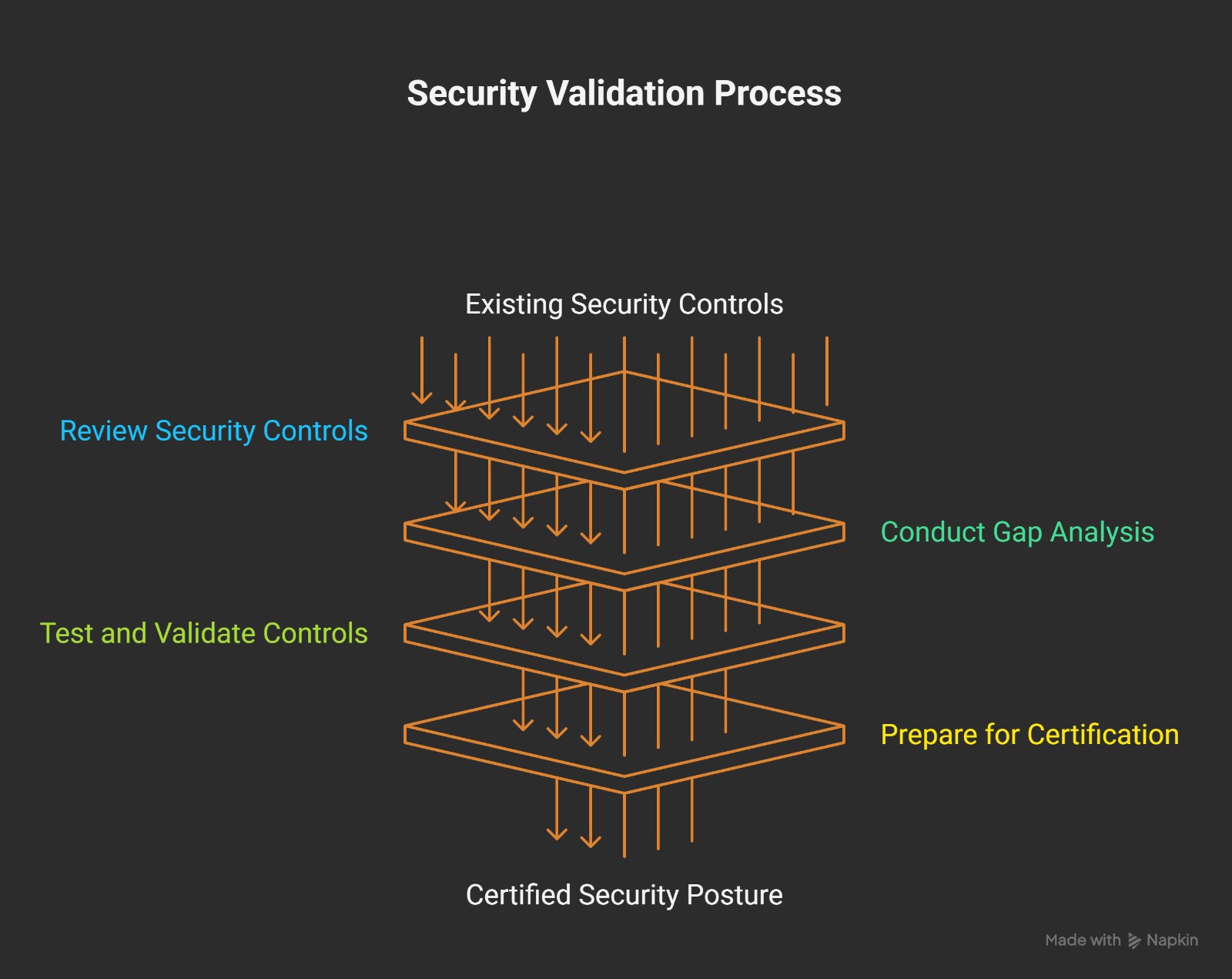
Validation Services
Our validation services ensure that your security measures meet industry standards and regulatory requirements, providing assurance that your industrial systems are adequately protected.
Key Benefits
- Verification of security control effectiveness
- Compliance with industry standards (IEC 62443, etc.)
- Documentation for regulatory requirements
- Independent verification of security posture
Our Process
- 1Review of existing security controls
- 2Compliance gap analysis
- 3Control testing and validation
- 4Certification preparation assistance
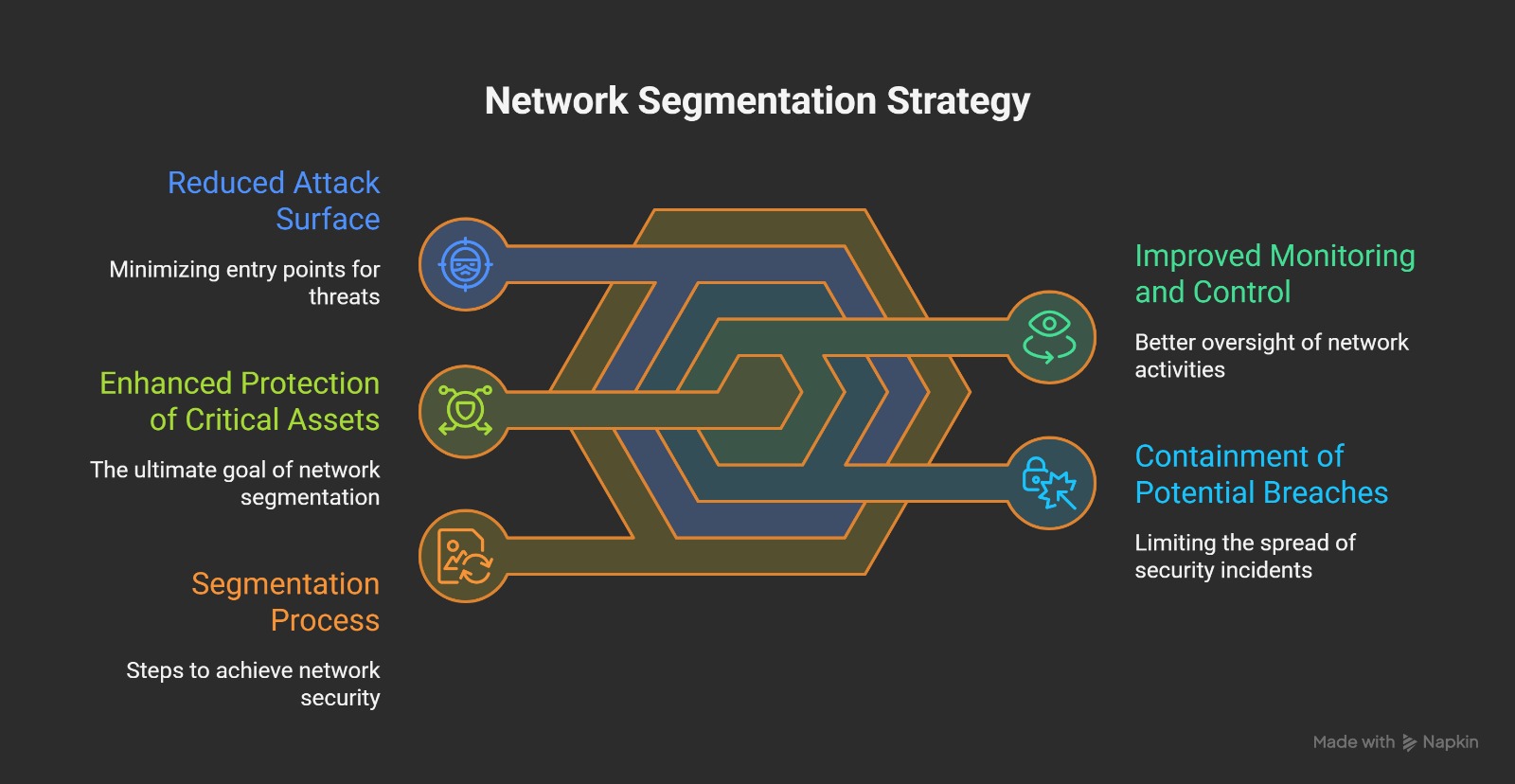
Network Segmentation
Our network segmentation services help you design and implement effective strategies to isolate critical systems and limit the potential impact of security breaches.
Key Benefits
- Reduced attack surface and lateral movement
- Containment of potential breaches
- Improved monitoring and control
- Enhanced protection of critical assets
Our Process
- 1Network architecture review
- 2Zone and conduit modeling
- 3Segmentation strategy development
- 4Implementation guidance and validation
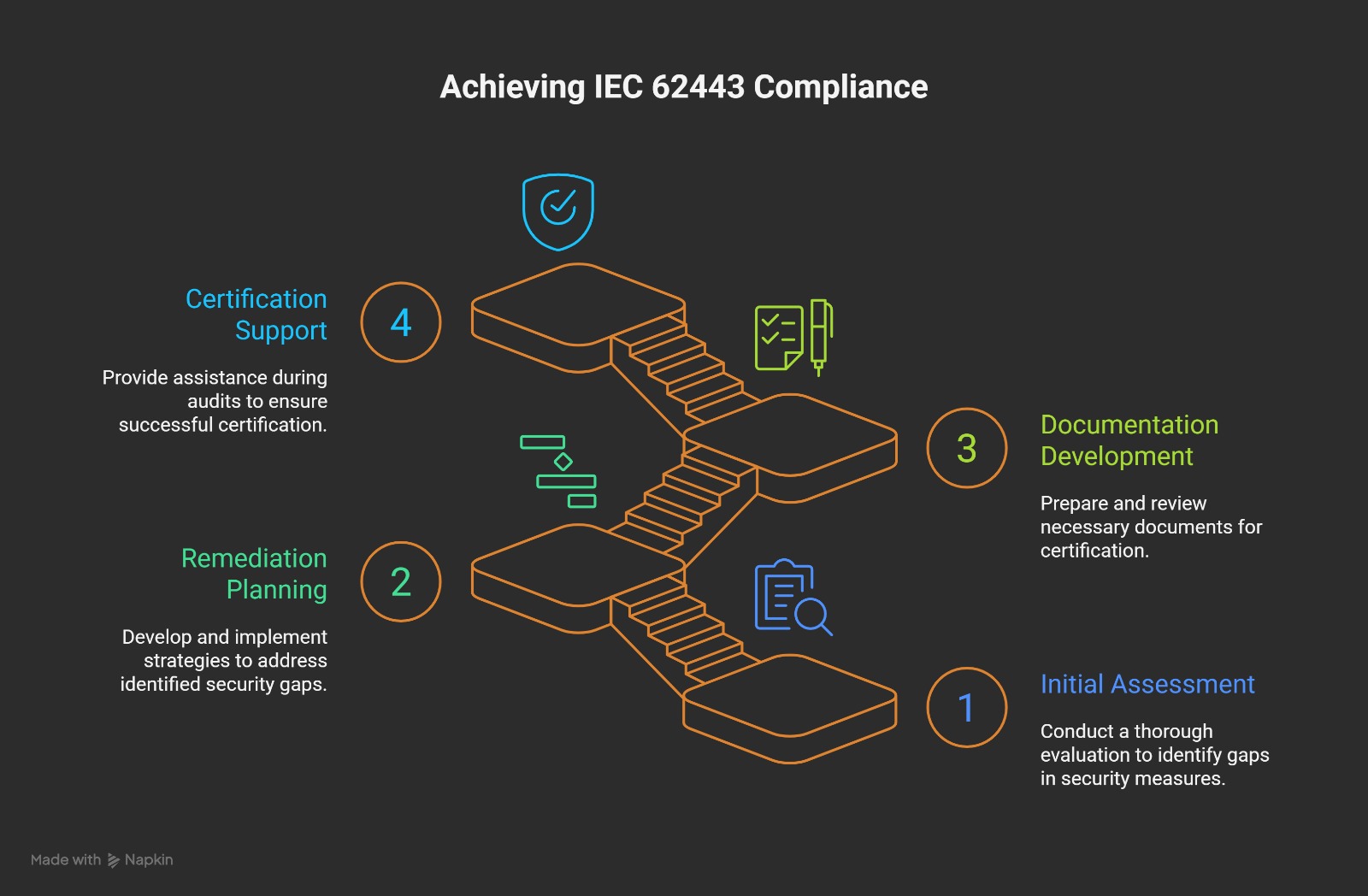
IEC 62443 Certification Facilitator
Our certification facilitation services guide organizations through the process of achieving IEC 62443 compliance, the international standard for industrial automation and control systems security.
Key Benefits
- Expert guidance through the certification process
- Gap analysis against IEC 62443 requirements
- Documentation preparation and review
- Pre-certification readiness assessment
Our Process
- 1Initial assessment and gap analysis
- 2Remediation planning and implementation support
- 3Documentation development and review
- 4Certification preparation and support during audits
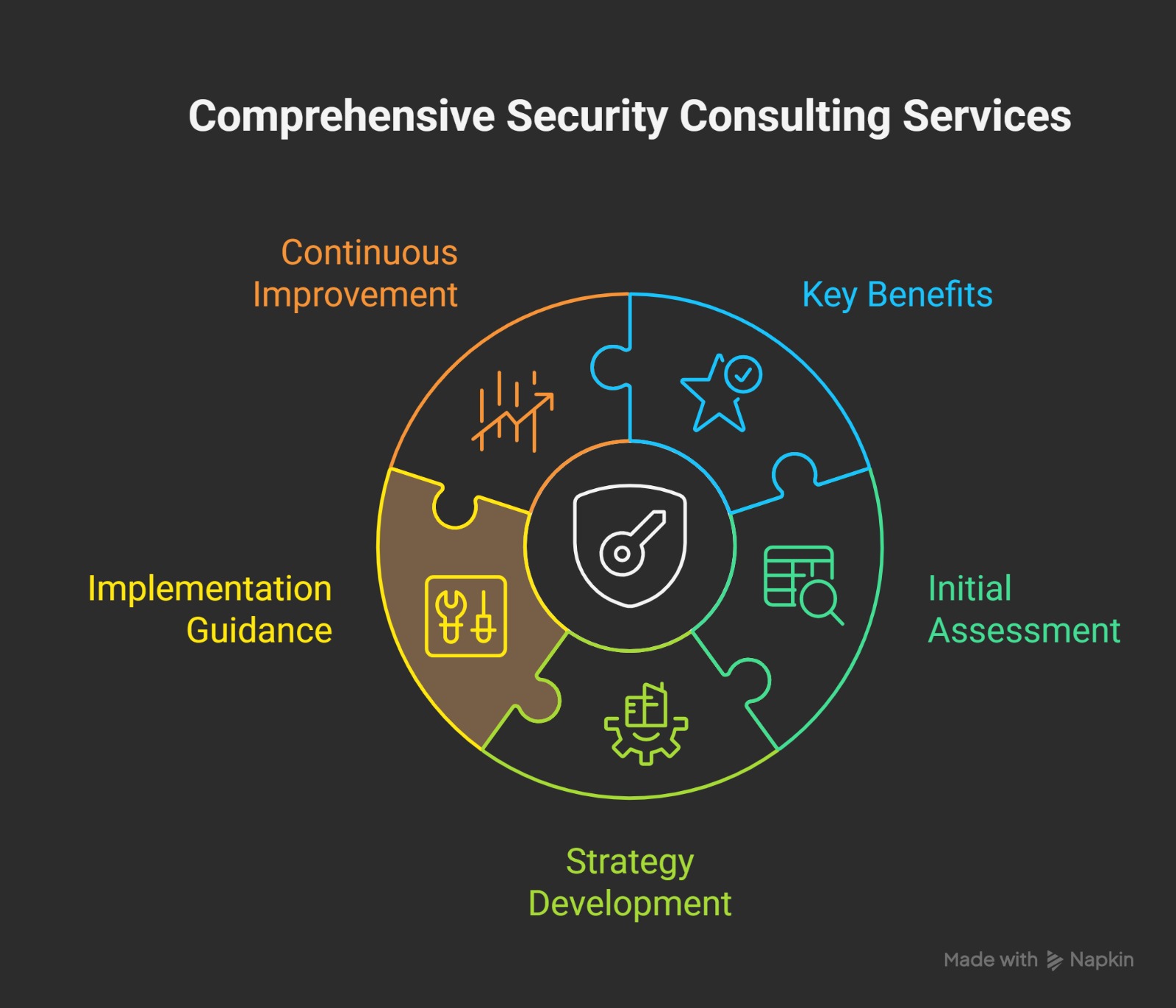
Security Consulting
Our security consulting services provide expert guidance on implementing robust security measures tailored to your specific industrial environment and business needs.
Key Benefits
- Access to specialized industrial cybersecurity expertise
- Customized security strategies
- Guidance on best practices and standards
- Ongoing support and advisory services
Our Process
- 1Initial assessment and requirements gathering
- 2Strategy development and planning
- 3Implementation guidance and support
- 4Continuous improvement recommendations
Custom Security Development
Our custom security development services create tailored solutions to address unique security challenges in your industrial environment that cannot be solved with off-the-shelf products.
Key Benefits
- Tailored solutions for unique security challenges
- Integration with existing systems and processes
- Optimized performance for your specific environment
- Proprietary protection for your critical assets
Our Process
- 1Requirements analysis and specification
- 2Solution design and development
- 3Testing and validation
- 4Implementation and ongoing support
Security Training
Our security training programs help your team develop the knowledge and skills needed to effectively protect your industrial systems from cyber threats.
Key Benefits
- Enhanced security awareness among staff
- Development of specialized security skills
- Improved incident response capabilities
- Reduced human-factor security risks
Our Process
- 1Training needs assessment
- 2Customized curriculum development
- 3Interactive workshops and exercises
- 4Evaluation and continuous improvement
Ready to secure your industrial systems?
Our team of experts is ready to help you address your specific cybersecurity challenges. Contact us today to discuss how our services can protect your critical infrastructure.
Get in touch